The future rarely arrives with noise. It appears first as a whisper, a small shift in behaviour, a new protocol that feels unnecessary, a technology no one has time to care about. Then quietly, it becomes the new default. In Identity and Access Management (IAM), we’re standing at one of those turning points, where the next decade is already visible to those who know where to look.
This edition breaks down future-shaping concepts, the technologies positioning themselves to rewrite identity infrastructure, and which sectors must prepare now to avoid being left behind.
What the Future Looks Like for IAM
IAM is evolving from access control to dynamic digital identity ecosystems driven by AI, distributed consensus and zero-trust design. Three shifts are already underway:
1. Quantum-Resistant Identity Security
Quantum computing threatens current encryption models. IBM’s Osprey and Google’s Sycamore already simulate workloads that classical systems can’t match. IAM must transition to post-quantum cryptography and key rotation frameworks before quantum scale breaks authentication open.
2. Identity Mesh as the New Foundation
Central IAM cannot handle identity sprawl; workloads, APIs, ML agents, and machine identities outnumber humans.
Identity Mesh distributes enforcement, unifies signals and allows decisions in real time, not at one slow central gate.
3. AI-Supervised Access Intelligence
IAM is moving toward predictive authorisation.
Systems will soon not only verify identity but also forecast intent, detect anomalies before breach, and self-correct risk paths without human approval.
These are not future ideas; they are early signals of where authentication is heading.
Sectors That Must Adapt First
Some industries will feel this future sooner than others. High-velocity environments with sensitive identity data stand at the frontline.
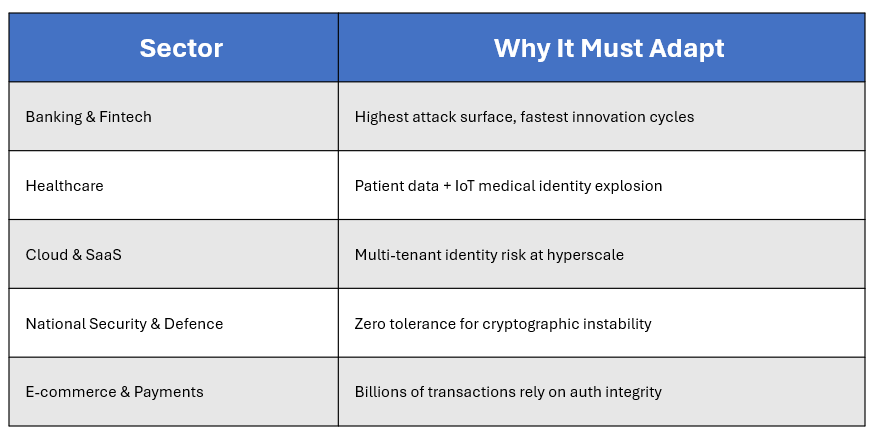
By 2027, compliance frameworks will likely mandate machine identity governance, quantum-safe encryption, and continuous authentication visibility across these sectors.
A Glitch-Free Future: What Gets Us There
To step into the next cycle without friction, enterprises must evolve from tools to architecture thinking.
The solution isn’t “better IAM”.
The solution is:
- Identity Mesh adoption
- Post-Quantum cryptography migration
- AI-layered behavioural anomaly detection
- Passwordless, phishing-resistant authentication
- Machine identity lifecycle automation
- Interoperable policy orchestration across environments
A glitch-free future is not the absence of threat; it is the presence of predictive defence.
Conclusion: Spot the Future, Don’t Wait for It
The organisations that win the next decade won’t be those who adapt late, but those who spot the shift early.
Identity is becoming fluid, predictive and distributed. Technology is becoming quantum-aware, intent-driven and self-correcting. The question isn’t what the future will be. It’s who will be ready when it arrives.