The Identity Problem No One Can Ignore
For decades, identity systems were built in silos.
One enterprise.
One directory.
One authentication domain.
That model worked when organisations operated within clearly defined network boundaries. Employees accessed systems from corporate offices, applications were hosted on internal servers, and identity governance was largely centralised.
That world no longer exists.
Modern enterprises now operate within highly distributed digital ecosystems where identities extend far beyond employees and internal systems. Businesses rely on cloud platforms, digital partners, remote teams, APIs, and machine identities that interact across multiple environments simultaneously.
Today’s enterprise operates across:
- Hybrid cloud platforms supporting critical workloads and distributed infrastructure
- SaaS ecosystems delivering enterprise applications such as CRM, HR, and financial systems
- API-driven integrations connecting digital services, microservices, and third-party applications
- Remote and hybrid workforces accessing systems from anywhere in the world
- Partner networks and supply chains requiring controlled identity federation and access governance
- Cross-border regulatory environments requiring compliance with frameworks such as GDPR and digital identity standards
Despite this transformation, many organizations still rely on fragmented identity architecture. Legacy identity systems were never designed to support modern Identity and Access Management (IAM) demands such as cloud identity governance, machine identity management, and cross-platform authentication.
This fragmentation introduces several structural challenges:
- Inconsistent Identity Governance
Multiple identity repositories create gaps in access visibility, increasing the risk of privilege misuse and compliance failures. - Authentication Complexity
Users often manage multiple credentials across platforms, weakening overall authentication security and increasing phishing risks. - Limited Identity Interoperability
Disconnected identity systems prevent seamless integration across SaaS platforms, APIs, and enterprise environments. - Rising Cybersecurity Risk
Identity remains the primary attack surface in modern breaches, making fragmented IAM environments a major security liability.
From a CXO perspective, this is no longer an IT inconvenience. It is a strategic governance issue that affects digital resilience, regulatory readiness, and enterprise trust.
Identity interoperability is therefore not simply a technological improvement. It is becoming the core foundation of digital identity governance, Zero Trust architecture, and future-ready cybersecurity strategy.
The Real-Time Shift Toward Global Identity Standards
The momentum is visible.
The European Union is advancing eIDAS 2.0 and the European Digital Identity Wallet (EUDI), enabling citizens to use verifiable digital credentials across member states.
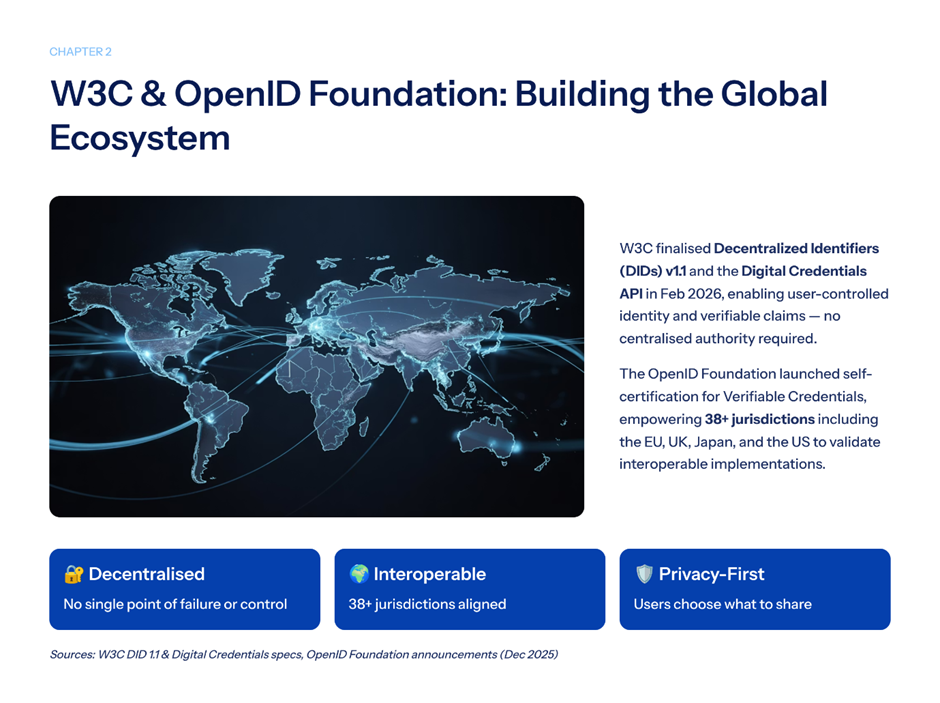
The World Wide Web Consortium (W3C) is standardizing Decentralized Identifiers (DID) and Verifiable Credentials.
The United States continues evolving digital identity guidance under NIST frameworks.
Across the Asia-Pacific, digital identity initiatives are being embedded into financial and regulatory systems.
This convergence reveals a clear direction:
Digital identity is moving from isolated enterprise systems to interoperable, cross-border infrastructure.
The surprising element?
Identity is becoming geopolitical.
Why Silos Are Breaking Enterprises
As organisations expand digitally, fragmented IAM environments create friction.
Common pain points include:
1. Duplicate Identity Repositories
- Multiple identity stores
- Inconsistent attribute definitions
- Conflicting access policies
This increases attack surfaces.
2. Compliance Complexity
Operating across regions means aligning with:
- GDPR
- eIDAS 2.0
- NIST standards
- Industry-specific regulations
Without interoperability, compliance becomes manual and reactive.
3. Vendor Lock-In
Proprietary IAM systems that cannot integrate:
- Limit scalability
- Increase migration costs
- Reduce architectural flexibility
Interoperability reduces dependency.
4. User Experience Friction
- Multiple logins
- Repeated identity verification
- Inconsistent authentication experiences
In a digital-first economy, friction drives attrition.
Zero Trust Demands Interoperability
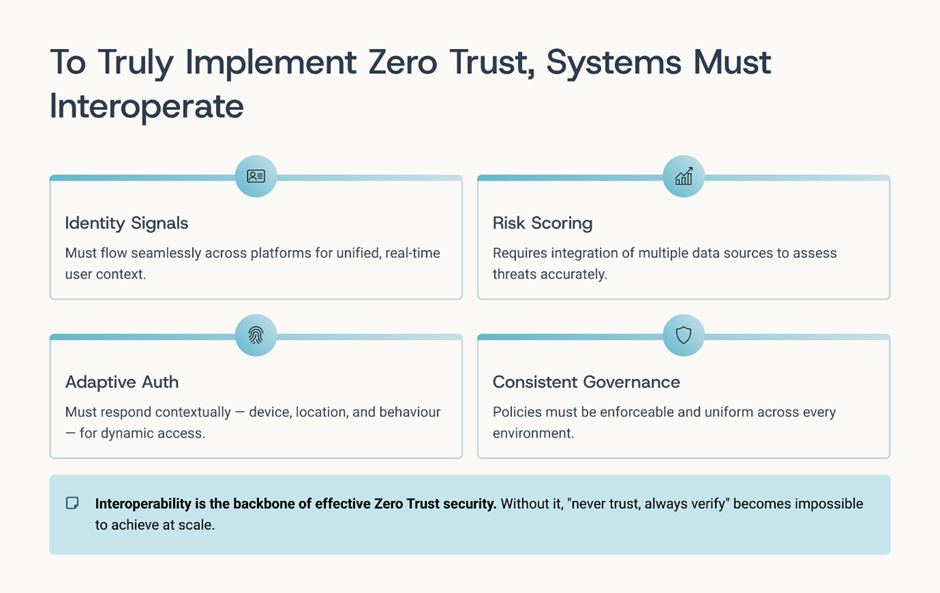
Zero Trust architecture assumes:
“Never trust. Always verify.”
But verification across disconnected systems is inefficient.
To truly implement Zero Trust:
- Identity signals must flow across platforms
- Risk scoring must integrate multiple data sources
- Authentication must adapt contextually
- Governance must remain consistent
Zero Trust without interoperability becomes isolated enforcement rather than unified defence. Interoperable identity ecosystems make adaptive security scalable.
The Rise of Decentralised Identity (DID)
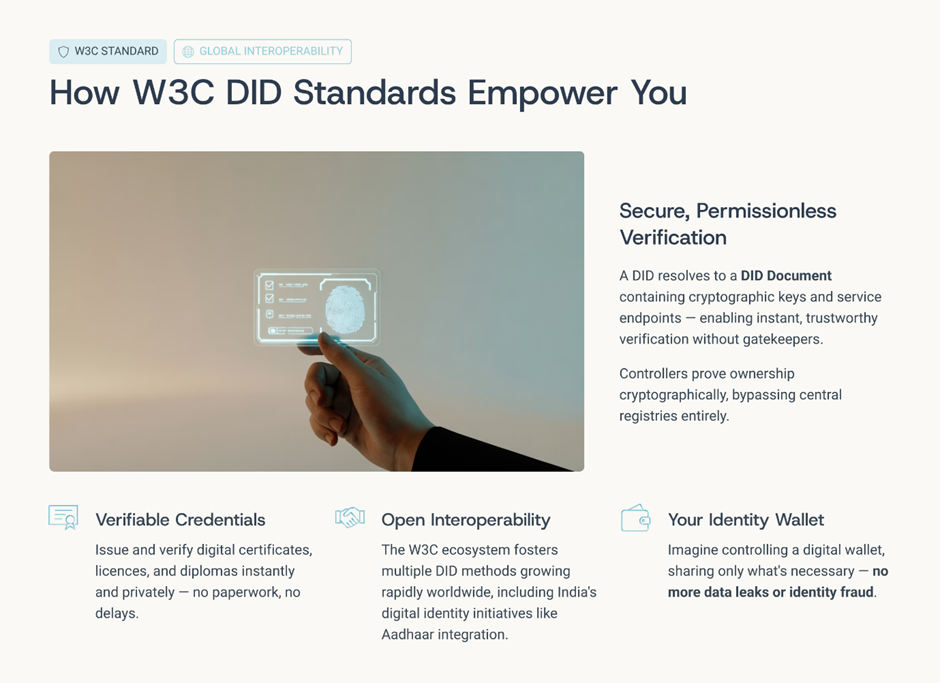
Decentralised identity frameworks represent a significant shift.
Under W3C DID standards:
- Individuals control their credentials
- Verifiable credentials replace static identifiers
- Authentication becomes cryptographically validated
- Data minimisation becomes practical
This reduces reliance on centralised identity stores.
For enterprises, this creates opportunity:
- Cross-platform identity portability
- Reduced data storage risk
- Enhanced privacy compliance
- Stronger authentication assurance
Interoperability is the enabler.
Identity Interoperability in Practice
From a CXO lens, interoperability is not theoretical.
It must translate into operational architecture.
This includes:
Standard-Based Federation

- SAML
- OAuth
- OpenID Connect
Enabling secure authentication across domains.
API-Level Identity Integration
- Token-based access
- Secure API gateways
- Identity-aware microservices
Supporting digital transformation.
Verifiable Credentials & Digital Wallets

- Portable identity proofs
- Cross-border credential recognition
- Reduced onboarding friction
Supporting global business mobility.
Machine Identity Governance
As automation expands:
- APIs
- Bots
- IoT devices
- Service accounts
Machine identities now outnumber human identities.
Interoperable governance is critical to manage them securely.
The Strategic Advantage of Interoperability
Organisations that prioritise identity interoperability gain:
1. Reduced Operational Risk
Unified governance reduces policy gaps.
2. Improved Regulatory Alignment
Standards-based systems adapt faster to evolving mandates.
3. Lower Long-Term Costs
Reduced duplication and simplified integration.
4. Enhanced Customer Trust
Seamless authentication experiences strengthen brand credibility.
5. Future-Ready Architecture
Open standards protect against obsolescence.
Interoperability is not merely technical alignment. It is strategic resilience.
The Emerging Identity Ecosystem
Looking forward, identity will likely evolve toward:
- Portable digital credentials
- Cross-platform authentication ecosystems
- Blockchain-anchored verifiable identity
- AI-driven identity risk scoring
- Unified human and machine identity governance
In this environment, isolation becomes vulnerability.
Interoperability becomes a competitive advantage.
The Risk of Waiting
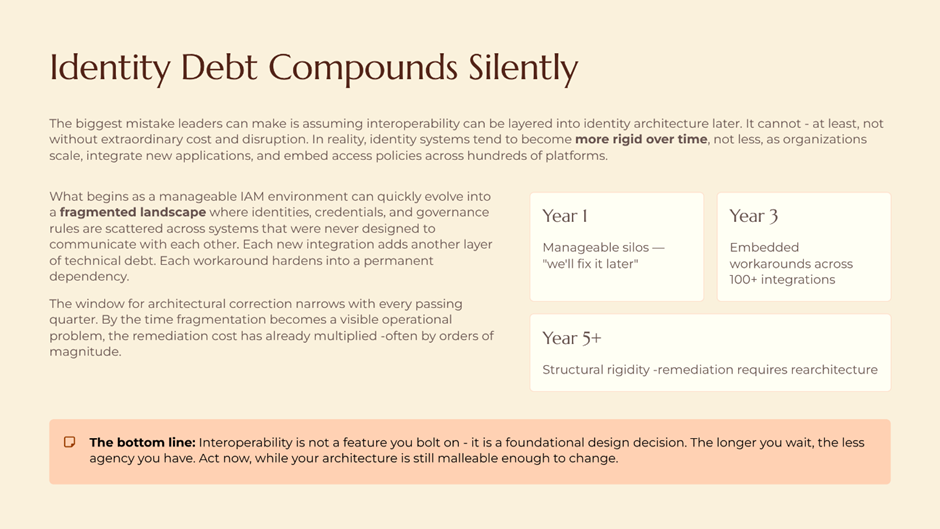
The biggest mistake leaders can make is assuming interoperability can be layered into identity architecture later. In reality, identity systems tend to become more rigid over time as organisations scale, integrate new applications, and embed access policies across hundreds of platforms. What begins as a manageable IAM environment can quickly evolve into a fragmented landscape where identities, credentials, and governance rules are scattered across systems that were never designed to communicate with each other.
As digital ecosystems grow, the cost and complexity of retrofitting interoperability increase significantly. Organisations often discover that identity silos are deeply tied to legacy applications, vendor-specific architectures, and compliance frameworks that resist rapid change. At that point, modernisation becomes less about improvement and more about disruption.
Several structural risks begin to emerge:
- Legacy Architecture Lock-In
Older IAM systems were designed for single-enterprise environments, not cloud-native or multi-platform ecosystems. Integrating them with modern identity standards often requires extensive reengineering. - Vendor Dependency Expansion
Proprietary IAM platforms can create long-term technological dependency, limit flexibility and make interoperability with emerging identity standards more difficult. - Escalating Compliance Demands
As regulations such as eIDAS 2.0 and global digital identity frameworks evolve, organisations without interoperable identity systems struggle to demonstrate regulatory readiness. - Operational Complexity Growth
Each additional identity repository, authentication system, or access policy adds operational overhead and increases the likelihood of governance gaps.
Designing interoperability from the beginning enables organisations to build identity architectures that remain adaptable as technology, regulation, and digital ecosystems continue to evolve.
A CXO Action Framework
For leaders preparing for the next phase of digital identity:
Assess Current Architecture
- Identify siloed identity repositories
- Map integration gaps
- Evaluate standards compliance
Prioritise Open Standards
- Support W3C DID
- Align with eIDAS 2.0 interoperability principles
- Embed OAuth and OpenID Connect
Strengthen Governance Integration
- Align IAM with enterprise risk management
- Integrate identity signals into SOC monitoring
- Elevate identity metrics to board reporting
Invest in Identity Modernisation
- Automate lifecycle management
- Implement adaptive authentication
- Prepare for decentralised identity integration
Interoperability must be intentional.
The Future of Digital Identity
We are moving toward a world where:
- A digital credential issued in one country is trusted in another.
- An enterprise identity flows seamlessly across SaaS platforms.
- Machine identities are governed as rigorously as human users.
- Privacy and portability coexist.
Identity will no longer belong to isolated systems.
It will belong to interoperable ecosystems.
The enterprises that lead this transformation will not only enhance security; they will enable borderless growth.
And from a CXO standpoint, the future belongs to organisations that design identity not as a gatekeeper, but as an intelligent, interoperable control plane powering global resilience.