The Shift Boards Can No Longer Ignore
For years, enterprise risk discussions revolved around financial controls, regulatory compliance, and operational resilience. Cybersecurity, while important, was often treated as a technical function; delegated to IT teams and reviewed periodically.
That model is now obsolete.
Today, most cyber incidents do not begin with sophisticated malware or advanced persistent threats. They begin with something far more fundamental: a failure in identity governance.
A compromised credential.
An overprivileged employee.
A third-party vendor with unchecked access.
These are not technical anomalies; they are governance failures.
Identity Governance and Administration (IGA) has emerged as one of the most critical control layers in modern enterprises. It is no longer just about managing access; it is about controlling business risk at scale.
What Is Identity Governance in Today’s Enterprise Context?
Identity Governance refers to the policies, processes, and technologies used to ensure that the right individuals have the right access to the right resources at the right time, and for the right reasons.
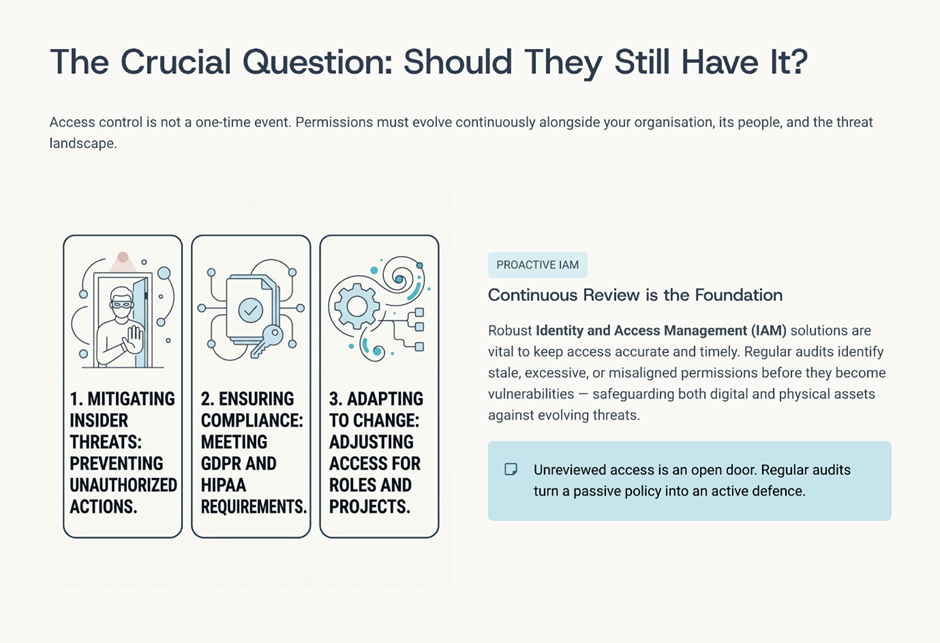
At its core, it answers three fundamental questions:
- Who has access?
- Why do they have it?
- Should they still, have it?
In a digital-first enterprise, where cloud systems, SaaS platforms, and remote work dominate, identity has effectively become the new perimeter.
Key Components of Identity Governance
- Access provisioning and de-provisioning
- Role-based access control (RBAC)
- Access reviews and certifications
- Segregation of duties (SoD) enforcement
- Privileged access management (PAM) integration
- Audit and compliance reporting
Without strong governance across these areas, organisations operate with invisible risk embedded within their access structures.
Why Identity Governance Has Become a Core Risk Control
Identity Is the Primary Attack Vector

Modern threat actors are not breaking down doors; they are logging in.
- A significant percentage of breaches involve stolen or compromised credentials
- Attackers increasingly use phishing, credential stuffing, and MFA fatigue attacks
- Once inside, they move laterally using legitimate access
This makes identity the most efficient and least detectable attack path.
Explosion of Digital Identities
Enterprises today manage:
- Employees across geographies
- Contractors and gig workers
- Third-party vendors and partners
- Machine identities (APIs, bots, service accounts)
Each identity represents a potential entry point.
Without governance, organizations face:
- Identity sprawl
- Orphaned accounts
- Excessive privileges
Overprivileged Access Is a Silent Threat
One of the most overlooked risks is the accumulation of access over time.
Employees change roles, projects evolve, systems expand, but access is rarely revoked.
This leads to:
- Users having more access than required
- Increased blast radius in case of compromise
- Difficulty in tracking accountability

In many breaches, the attacker succeeds not because access was gained, but because too much access already existed.
Third-Party and Supply Chain Exposure
Vendors and partners often require system access, but:
- Their access is rarely monitored with the same rigour
- Governance policies may not extend fully to third-party identities
- Compromise of one vendor can impact multiple systems
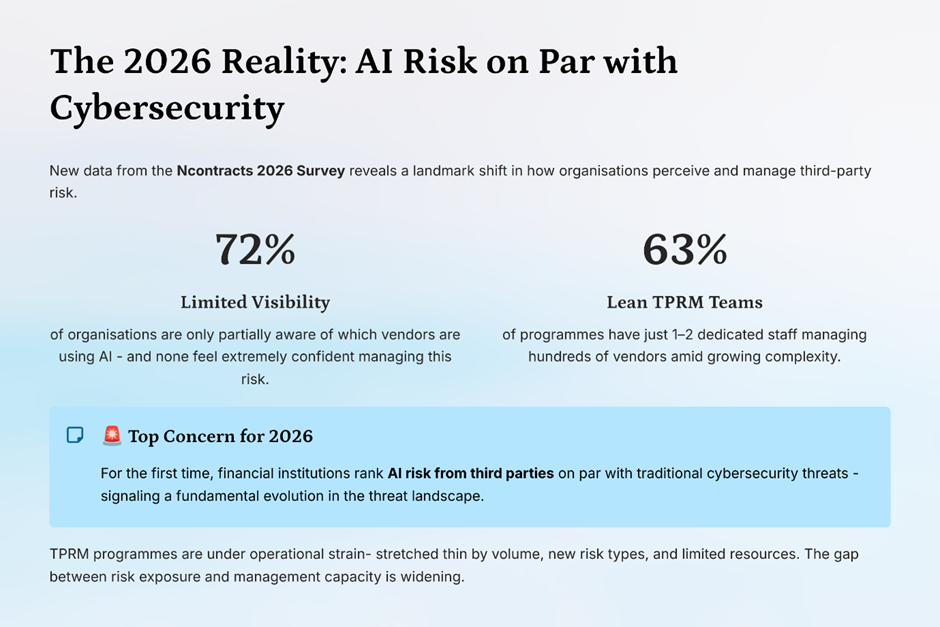
This expands the enterprise attack surface beyond organisational boundaries.
Real-World Context: How Identity Failures Translate to Business Risk
From a CXO perspective, identity failures are not just security incidents; they are business events.
Common Business Impacts
- Operational disruption
Systems go offline, services halt, productivity drops - Financial loss
Ransom payments, recovery costs, revenue impact - Regulatory penalties
Non-compliance with frameworks like GDPR, SOX, HIPAA - Reputational damage
Loss of customer trust and investor confidence - Strategic setbacks
Delayed growth initiatives due to security concerns
The key realisation for leadership is this:
Identity risk is enterprise risk.
The CXO Perspective: Reframing Identity Governance
For executive leadership, identity governance must be viewed through a strategic lens, not an operational one.
What CXOs Should Prioritise
- Visibility over identities and access across the enterprise
- Alignment between business roles and access rights
- Continuous monitoring, not periodic reviews
- Integration with broader risk and compliance frameworks
- Automation to reduce human error and inefficiency
Key Strategic Questions for Leadership
Instead of asking:
- “Are our systems secure?”
Boards and CXOs should be asking:
- Do we have complete visibility into who has access to critical systems?
- Are access rights aligned with current roles and responsibilities?
- How quickly can we revoke access in case of a risk event?
- How are we managing third-party identities?
- Is identity governance integrated into our enterprise risk framework?

Future Risk Landscape: Where Identity Risk Is Headed
Identity risk is not static; it is evolving rapidly alongside technology.
AI-Driven Identity Attacks

- Deepfake-based social engineering
- AI-generated phishing campaigns
- Automated credential harvesting
Attackers will increasingly use AI to exploit identity systems at scale.
Decentralised Workforces
- Remote work and hybrid environments
- Access from unmanaged devices and networks
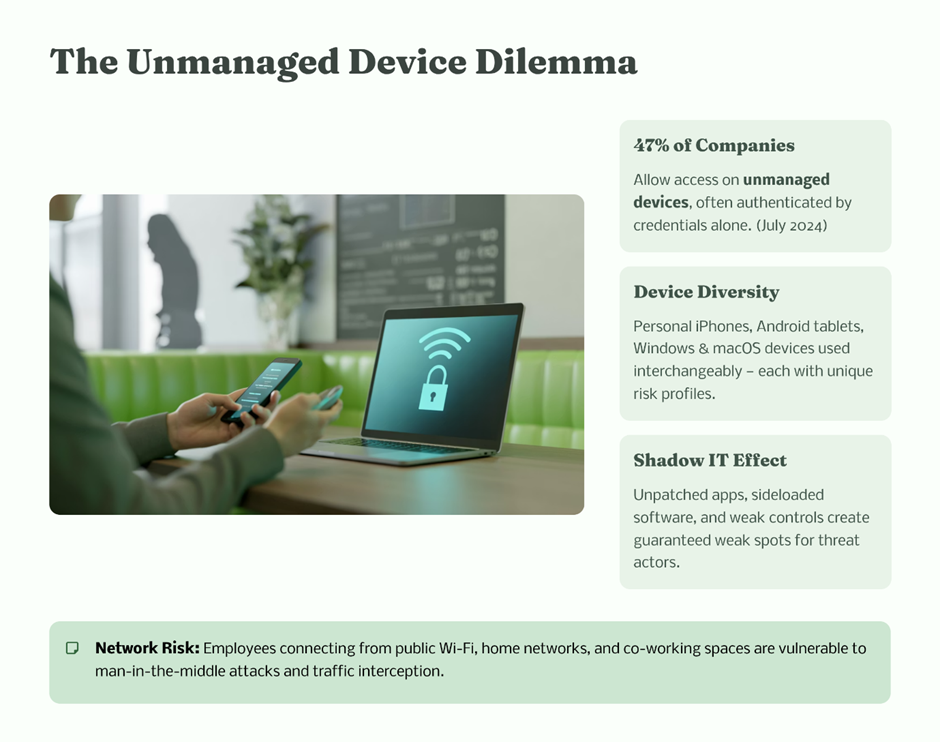
This reduces traditional perimeter controls and increases reliance on identity-based security.
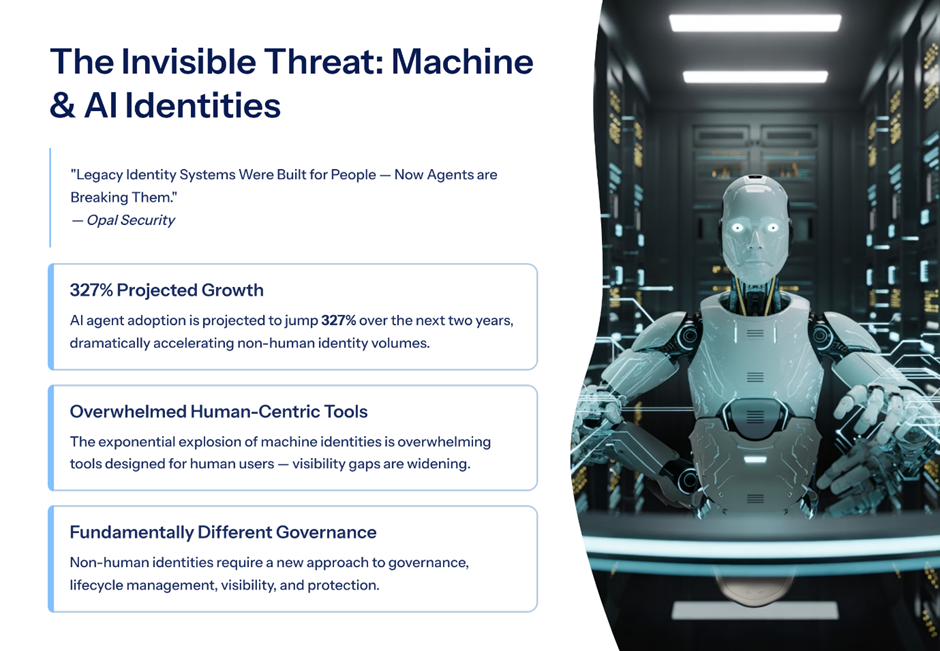
Machine Identities Outnumbering Human Identities
- APIs, bots, and service accounts are growing exponentially
- Many are unmanaged and poorly monitored
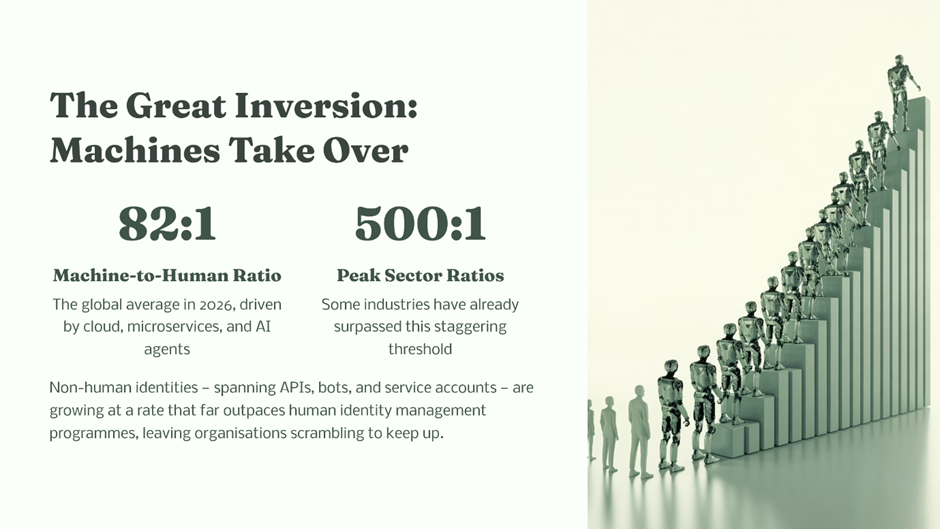
Machine identities will become a major blind spot in governance frameworks.
Regulatory Pressure on Identity Controls
Regulators are increasingly focusing on:
- Access governance
- Identity lifecycle management
- Auditability of access decisions

Organisations without mature identity governance will face heightened compliance scrutiny.
Zero Trust Becoming the Standard
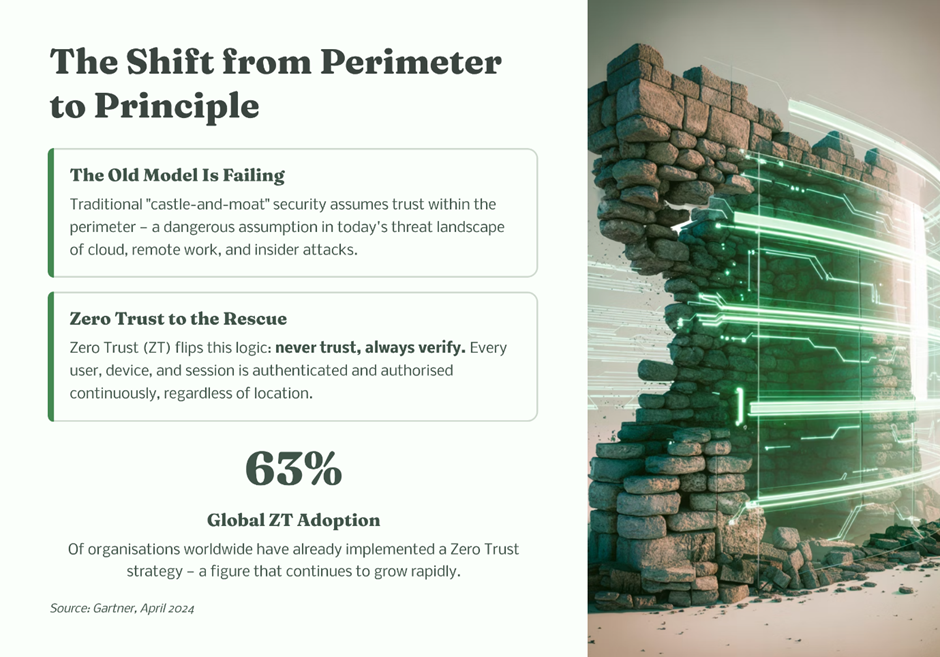
Zero Trust architecture is built on one principle:
Never trust, always verify.
Identity governance is the foundation of Zero Trust, ensuring:
- Continuous authentication
- Context-aware access
- Least privilege enforcement
Building a Future-Ready Identity Governance Framework
To address emerging risks, organisations must evolve from static governance models to dynamic, intelligence-driven systems.
Core Capabilities to Invest In
- Automated access provisioning and de-provisioning
- AI-driven anomaly detection for identity behaviour
- Continuous access certification
- Privileged access monitoring
- Unified identity platforms across cloud and on-prem systems
Best Practices for Enterprises
- Implement least privilege access by default
- Conduct regular access reviews with business ownership
- Extend governance to third-party and machine identities
- Integrate identity governance with security operations (SOC)
- Establish clear accountability for access decisions
The Board’s Role: From Oversight to Ownership
Boards play a critical role in shaping how identity risk is managed.
Traditionally, cybersecurity has been a reporting function to the board.
That is no longer sufficient.
What Boards Must Do
- Treat identity governance as a core enterprise risk control
- Ensure it is embedded in risk management frameworks
- Demand metrics and visibility into identity-related risks
- Align identity governance with business strategy and growth
Key Metrics Boards Should Monitor
- Number of orphaned or inactive accounts
- Percentage of users with excessive privileges
- Time taken to revoke access after role change
- Coverage of access reviews and certifications
- Third-party access exposure levels
Conclusion: A Strategic Opportunity, Not Just a Risk
Identity governance is often discussed in the context of risk mitigation, but it also presents a strategic opportunity.
Organisations that invest in strong identity governance can:
- Enable secure digital transformation
- Build trust with customers and partners
- Improve operational efficiency
- Strengthen regulatory compliance posture
For boards and CXOs, the path forward is clear.
Identity governance is no longer a backend control managed by IT.
It is a frontline defence mechanism and a strategic business enabler.
The future
In an era where access defines capability, control over identity defines resilience.
The organisations that recognise this shift and act on it will not only prevent breaches but will also position themselves as trusted, secure, and future-ready enterprises.