I. Introduction: The Startup Dream and the Hidden Risk
Every tech founder starts with a vision.
Build fast. Scale quickly. Disrupt industries.
But while founders obsess over product launches, fundraising, AI innovation, and user growth, one silent risk keeps growing in the background:
Cyber exposure.
The uncomfortable reality is that modern startups are no longer attacked for being large.
They are attacked because they are highly connected, fast-moving, and often underprepared.
From SaaS platforms and cloud environments to AI-powered tools and remote teams, startups operate inside digital ecosystems that expand risk every single day.
And one breach today can destroy years of growth momentum overnight.
This is why cybersecurity is no longer an IT discussion.
It is a founder-level business survival strategy.
II. The Current Cyber Landscape: Why Founders Should Pay Attention
The global cybersecurity environment has changed dramatically.
Recent data shows:
- Cybercrime is expected to cost the global economy over $23 trillion annually by 2027
- More than 80% of breaches involve compromised identities or stolen credentials
- AI-driven phishing attacks are increasing rapidly across startup ecosystems
- Supply chain and third-party attacks are now among the fastest-growing risks

At the same time, geopolitical cyber conflicts involving critical infrastructure and digital platforms have revealed how vulnerable interconnected systems truly are.
Cybersecurity is no longer just about protecting servers.
It is about protecting:
- Customer trust
- Investor confidence
- Operational continuity
- Enterprise value
III. Why Tech Founders Are Especially Vulnerable
Most startups unintentionally create cybersecurity risk while trying to scale faster.
- Speed Becomes More Important Than Governance
Founders prioritize:
- Product development
- Hiring
- Customer acquisition
- Revenue growth
Security controls are often delayed because they are seen as “later-stage priorities.”
But cyber risk compounds silently.
2. SaaS Sprawl Creates Visibility Gaps

Modern startups rely on dozens of tools:
- CRM platforms
- Cloud collaboration apps
- AI automation systems
- Payment platforms
- Third-party APIs
Over time, nobody clearly knows:
- Who has access
- Why do they have access
- Whether the access is still necessary
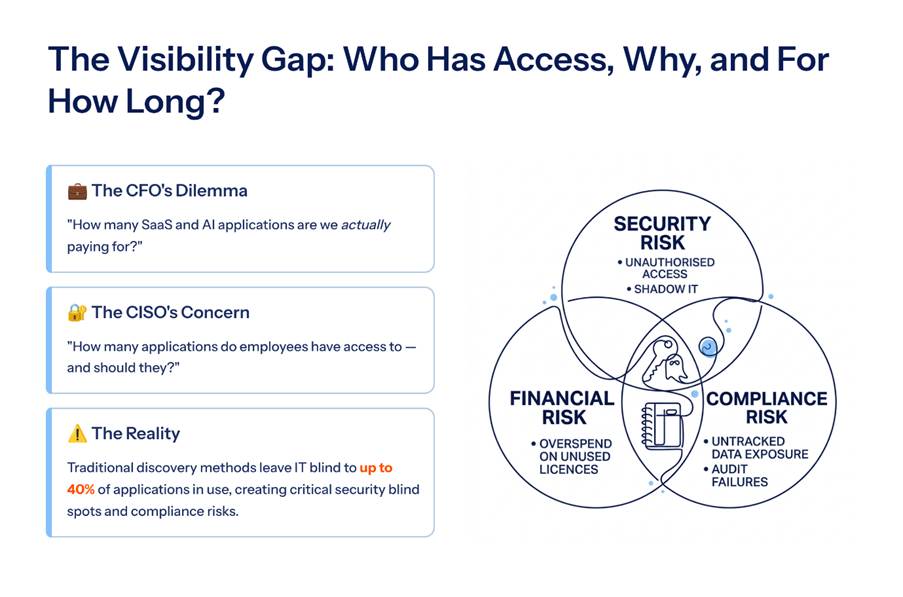
This creates dangerous identity exposure.
3. Identity Is the New Attack Surface

The biggest misconception founders still have:
Cyberattacks start with hacking infrastructure.
In reality, most breaches start with:
- Weak passwords
- Overprivileged access
- Shared credentials
- Phishing attacks
- Unmanaged identities
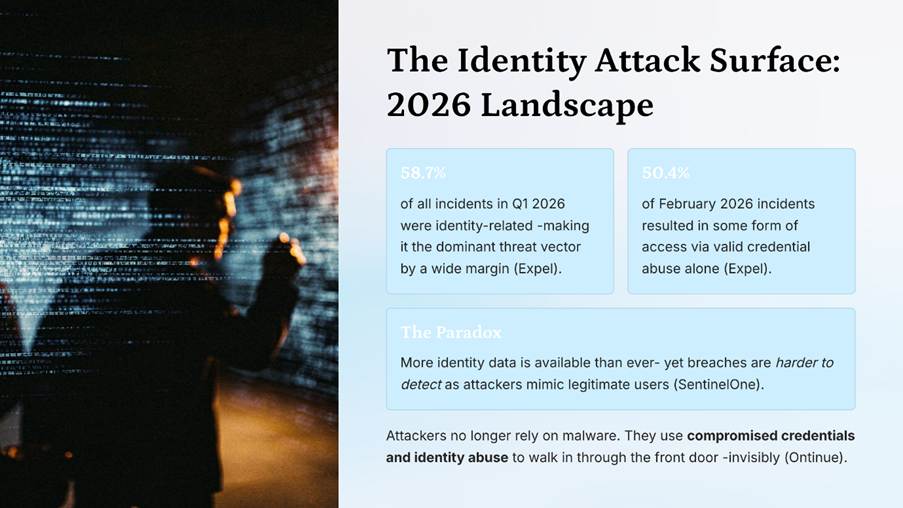
Attackers no longer “break in.”
They simply log in.
IV. The Cybersecurity Playbook Every Founder Needs
The smartest startups are not waiting for breaches to mature their cybersecurity posture.
They are building security into scale from day one.
1. Make Identity and Access Management (IAM) the Foundation
Identity is now the centre of cybersecurity.
Every founder should prioritise:
- Single Sign-On (SSO)
- Multi-Factor Authentication (MFA)
- Role-based access control
- Identity Governance
Why This Matters
A single compromised credential can expose:
- Customer databases
- Financial systems
- Product infrastructure
- Internal communications
Strong IAM reduces risk before attackers gain momentum.
2. Adopt the Principle of Least Privilege
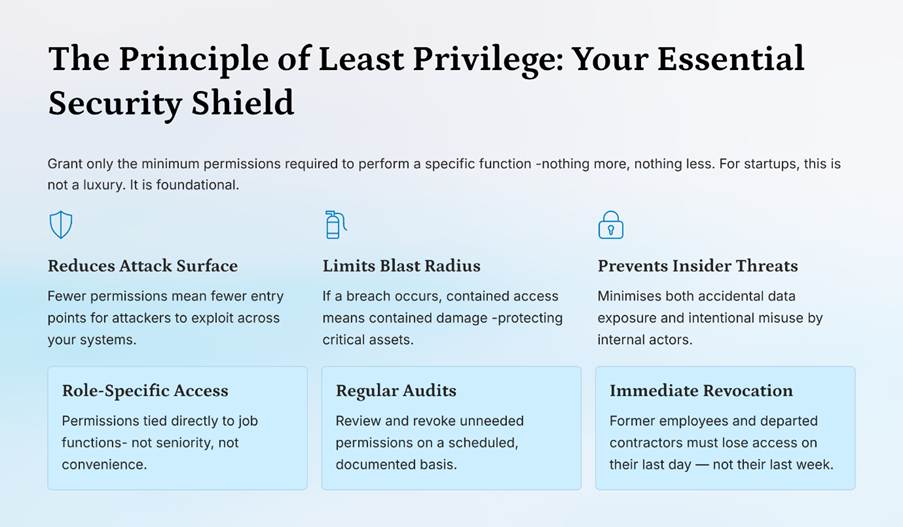
One of the most overlooked startup risks is excessive access.
Employees, contractors, and vendors often receive permissions they no longer need.
Founders should ensure:
- Access is role-specific
- Permissions are reviewed regularly
- Former employees lose access immediately
The less access available, the smaller the blast radius during a breach.
3. Build Visibility Before Complexity Explodes
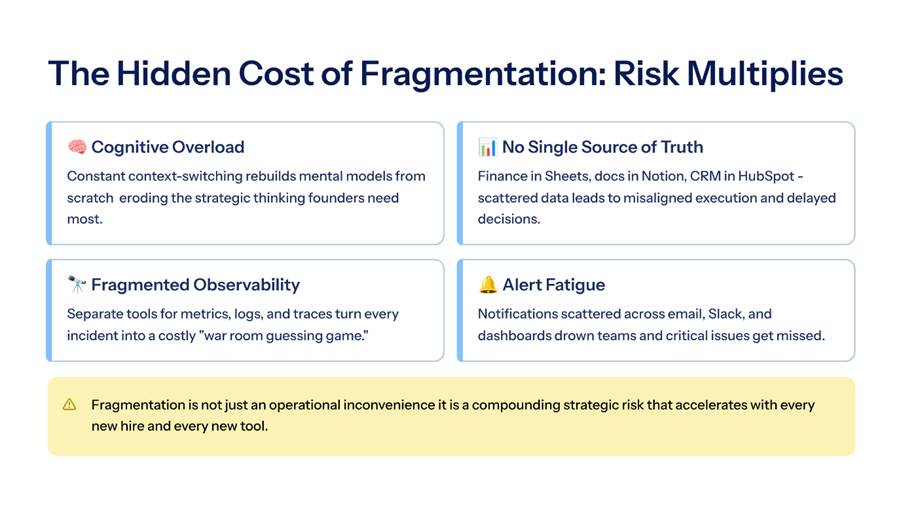
As startups grow, systems become fragmented quickly.
Without visibility, risk multiplies.
Founders should prioritise:
- Centralised monitoring
- Cloud visibility
- Third-party access tracking
- Real-time activity alerts
Cybersecurity failures often happen because organisations simply cannot see their exposure clearly.
4. Secure Third-Party and Vendor Access
Startups operate inside interconnected ecosystems.
Every external integration introduces risk.
This includes:
- Vendors
- Developers
- Payment providers
- Marketing platforms
- AI tools
Many modern breaches originate from trusted external access points.
Third-party governance is no longer optional.
5. Train Teams Before Attackers Do
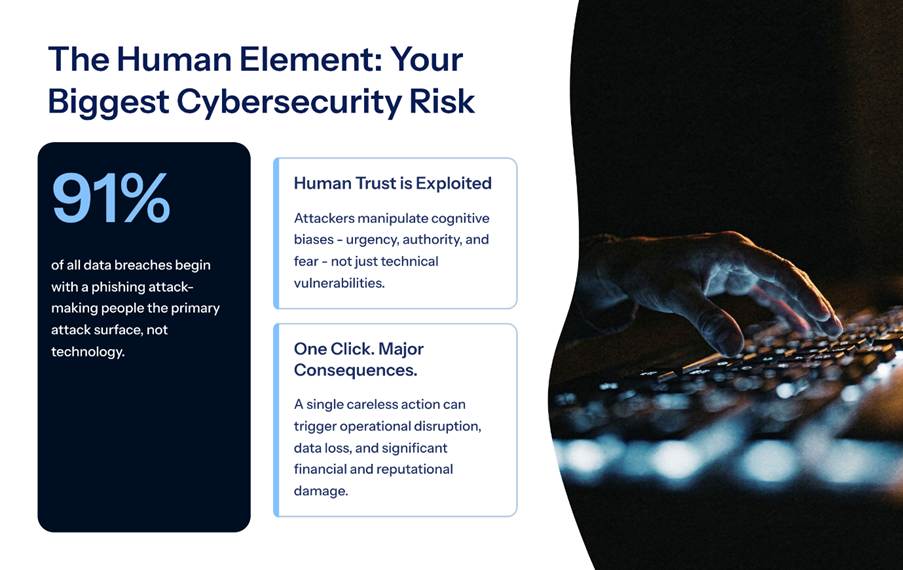
Human behaviour remains one of the biggest cybersecurity vulnerabilities.
Employees should understand:
- Phishing risks
- Credential security
- Access responsibility
- Secure collaboration practices
A single careless click can trigger operational disruption.
Cybersecurity awareness is no longer technical training.
It is operational readiness.
6. Prepare for Breaches Before They Happen
The question is no longer:
“Will a breach happen?”
The real question is:
“How prepared are we when it does?”
Every startup should have:
- Incident response plans
- Backup strategies
- Crisis communication frameworks
- Recovery protocols

Organisations recover faster when preparation already exists.
V. The Hidden Business Cost of Weak Cybersecurity
Founders often underestimate the true impact of cyber incidents.
The damage extends far beyond technology.
1. Customer Trust Collapses Quickly
Users may forgive product delays.
They rarely forgive exposed data.
Trust, once lost, becomes extremely difficult to rebuild.
2. Investor Confidence Changes Immediately
Security incidents trigger concerns around:
- Governance
- Operational maturity
- Scalability
- Leadership discipline

Cybersecurity now directly impacts funding conversations.
3. Enterprise Sales Become Harder
Large clients increasingly demand:
- Security assessments
- Compliance proof
- Identity governance standards

Weak security slows partnerships and revenue opportunities.
VI. How AI Is Changing the Threat Landscape
Artificial Intelligence is reshaping cybersecurity rapidly.
Attackers are using AI for:
- Advanced phishing campaigns
- Deepfake impersonation
- Automated reconnaissance
- Social engineering at scale
This means startups face more sophisticated threats earlier than ever before.
At the same time, AI can strengthen defence through:
- Behavioural analytics
- Threat detection
- Automated response systems
The difference lies in whether founders adopt cybersecurity strategically or reactively.
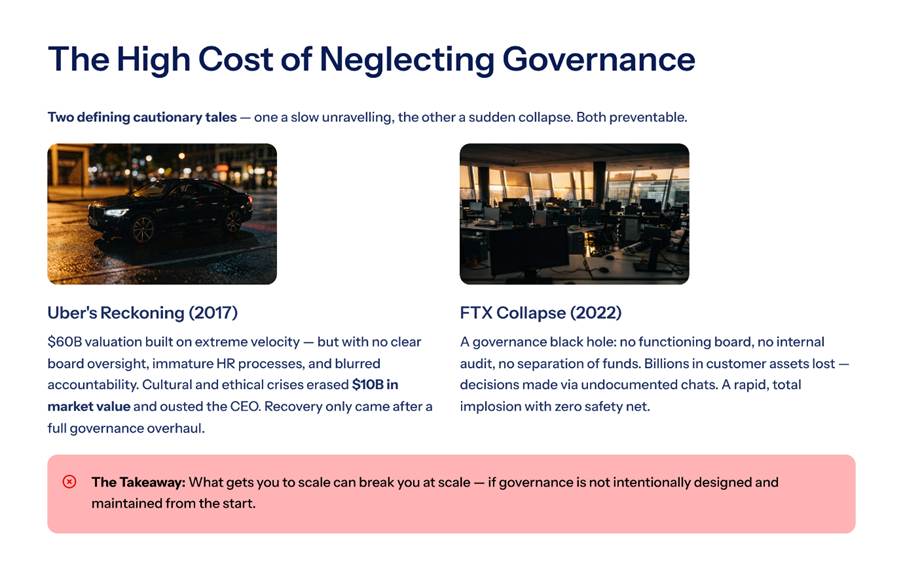
VII. The CXO Perspective: Why Leadership Matters
Cybersecurity is no longer a backend function.
It is now tied directly to:
- Business resilience
- Revenue continuity
- Digital trust
- Brand reputation
This is where a CXO mindset becomes critical.
Strong cybersecurity leadership helps startups:
- Align security with growth
- Govern identity effectively
- Build long-term resilience
- Scale without exposing the business
The most successful founders understand one important principle:
Security is not the opposite of growth.
It is what makes sustainable growth possible.
VIII. What Smart Startups Are Doing Differently
The next generation of resilient startups is already changing its approach.
They are:
- Embedding IAM early
- Prioritising Zero Trust frameworks
- Governing access continuously
- Monitoring third-party ecosystems
- Treating cybersecurity as a strategic business layer
This shift creates stronger trust with:
- Customers
- Investors
- Enterprise partners
And trust has become one of the most valuable business currencies.
IX. Future Outlook: Where Startup Cybersecurity Is Heading
The future will reward startups that build cybersecurity maturity early.
As digital ecosystems become more interconnected, startups will face increasing pressure from customers, investors, regulators, and enterprise partners to demonstrate stronger security accountability. Cybersecurity will no longer be viewed as a backend operational layer; it will become a visible indicator of business maturity and long-term resilience.

Key trends include:
- Identity-first security models
Organisations will increasingly focus on identity as the primary control layer. Access decisions will become smarter, more contextual, and continuously monitored. - AI-driven threat defence
AI will play a major role in identifying anomalies, detecting suspicious behaviour, and reducing response times in the face of evolving cyber threats. - Real-time access governance
Startups will move toward continuous monitoring of permissions, privileged accounts, and third-party access instead of periodic reviews. - Board-level cyber oversight
Investors and leadership teams will demand greater visibility into cyber risk, governance structures, and operational resilience. - Stronger third-party risk management
As startups depend heavily on external vendors, APIs, and SaaS platforms, third-party governance will become critical for maintaining digital trust. - Cybersecurity is becoming a competitive differentiator
Startups with strong security frameworks will gain faster enterprise trust, smoother compliance approvals, and stronger partnership opportunities.
Founders who delay cybersecurity may still scale fast.
But they may not scale sustainably.
Conclusion: Security Is No Longer Optional Growth Infrastructure
Tech founders are building the next generation of digital businesses.
But every digital business now depends on one critical factor:
Trust.
And trust depends on cybersecurity.
The startups that win in the next decade will not simply be the fastest innovators.
They will be the organisations that combine:
- Innovation
- Governance
- Identity control
- Operational resilience
Into one scalable strategy.
Final Thought
Cybersecurity is no longer something founders add later.
It is infrastructure.
It is governance.
It is business continuity.
And increasingly, it is the difference between startups that scale confidently and startups that collapse unexpectedly.