I. Why IAM Is Becoming the Centre of Enterprise Risk Management
For years, enterprise risk management (ERM) has revolved around financial controls, regulatory compliance, and operational resilience. Cybersecurity, while critical, was often treated as a technical layer; something owned by IT and periodically reviewed at the board level.
That framing no longer holds.
From a CXO’s perspective, the nature of enterprise risk has fundamentally changed. Today, the most significant threats to business continuity, reputation, and financial stability are increasingly tied to how identities are managed across the organisation.
A compromised credential can now disrupt operations.
An overprivileged account can expose sensitive data.
A third-party identity can become the entry point for a systemic breach.
This is why Identity and Access Management (IAM) is no longer a support function. It is rapidly becoming the central control point for enterprise risk management.
II. Understanding IAM in the Modern Enterprise Context
What IAM Really Means Today
IAM is not just about login systems or access requests. It is the framework that ensures:
- The right individuals have access
- To the right resources
- At the right time
- For the right reasons
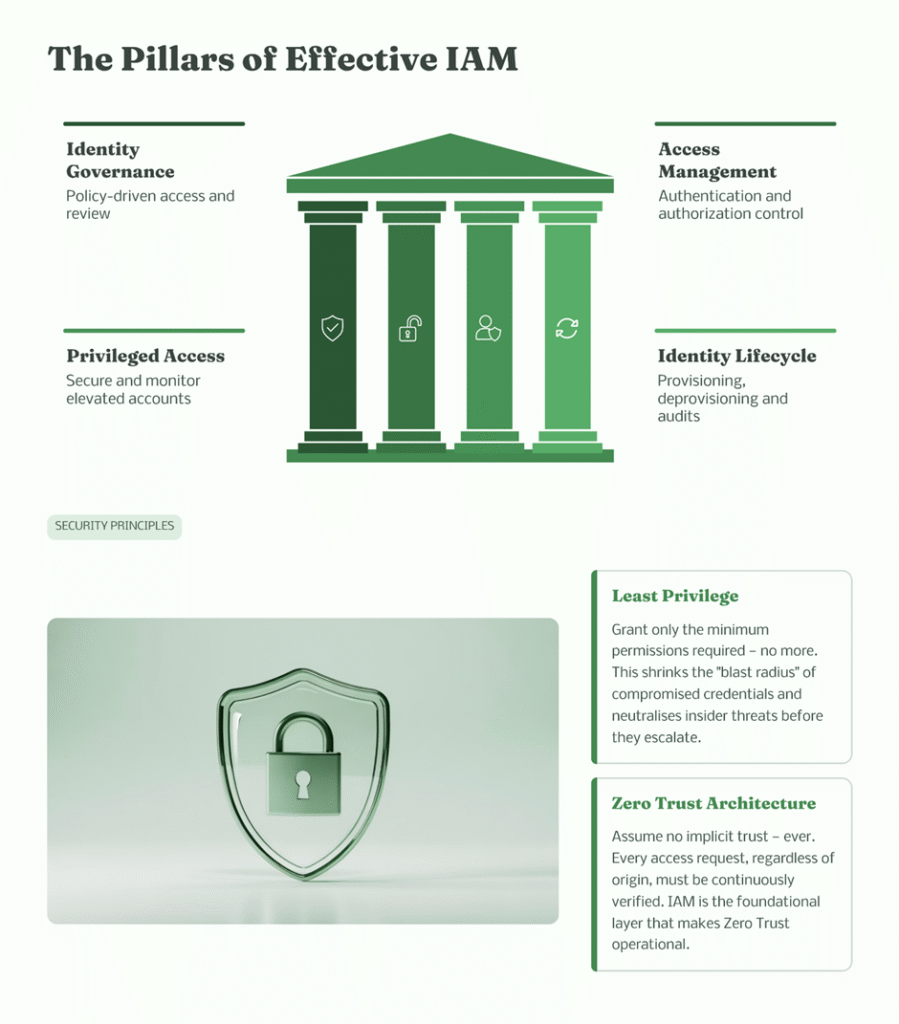
III. Core Components of IAM
To understand why Identity and Access Management sits at the centre of enterprise risk, it is essential to look beyond definitions and examine how its core components operate in a real-world business environment. Each layer is not just a technical control, but a risk management mechanism that directly influences security, compliance, and operational continuity.
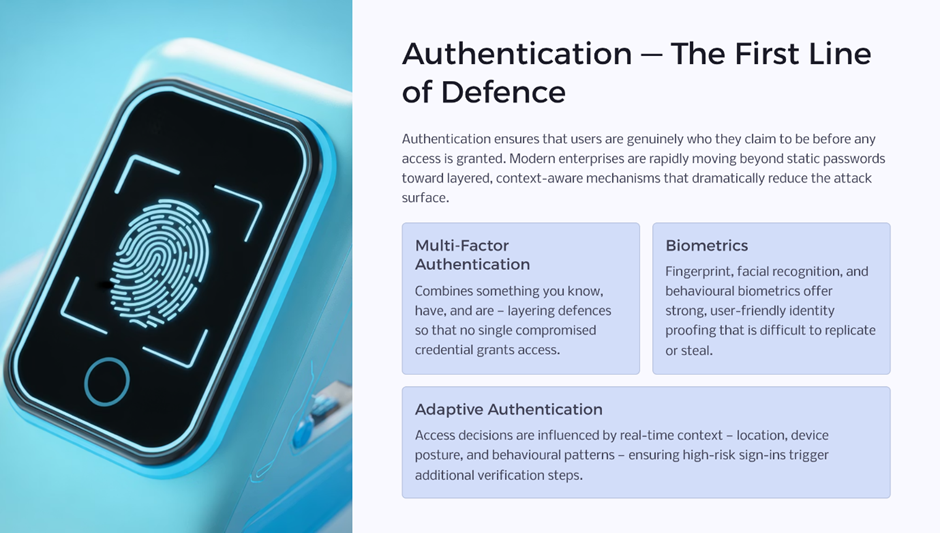
- Authentication (MFA, biometrics, adaptive authentication)
Authentication is the first line of defence, ensuring that users are genuinely who they claim to be. Modern enterprises are moving beyond passwords toward multi-factor and adaptive authentication, where access decisions are influenced by context such as location, device, and behaviour. This reduces the likelihood of credential-based attacks and strengthens trust at the point of entry. - Authorisation (role-based and attribute-based access control)
Once identity is verified, authorisation determines what that identity can do. Effective authorisation models enforce least-privilege access, ensuring users have only the permissions necessary for their roles. Poor authorisation leads to overprivileged environments, significantly increasing the impact of any compromised account. - Identity Governance (access reviews, certifications, lifecycle management)
Governance ensures that access remains appropriate over time. Through regular certifications, lifecycle management, and policy enforcement, organisations can prevent access creep and maintain alignment between business roles and system permissions. - Privileged Access Management (PAM)
Privileged accounts pose the highest risk. PAM solutions enforce strict controls, session monitoring, and just-in-time access to minimise misuse and detect anomalies early. - Single Sign-On (SSO)
SSO simplifies user experience while centralising access control. It reduces password fatigue and improves security by limiting the number of credentials users must manage. - Monitoring and auditing of identity activity
Continuous monitoring provides visibility into how identities interact with systems. This enables organisations to detect unusual behaviour, respond to threats in real time, and maintain audit readiness.
Together, these components form a cohesive framework that transforms identity from an access mechanism into a strategic risk control layer.
Why This Matters
In a digital enterprise:
- Identity is the new perimeter
- Access is the new control layer
- Governance is the new risk management mechanism
IV. The Real-World Shift: Identity at the Centre of Cyber Incidents
What the Data Is Showing Globally
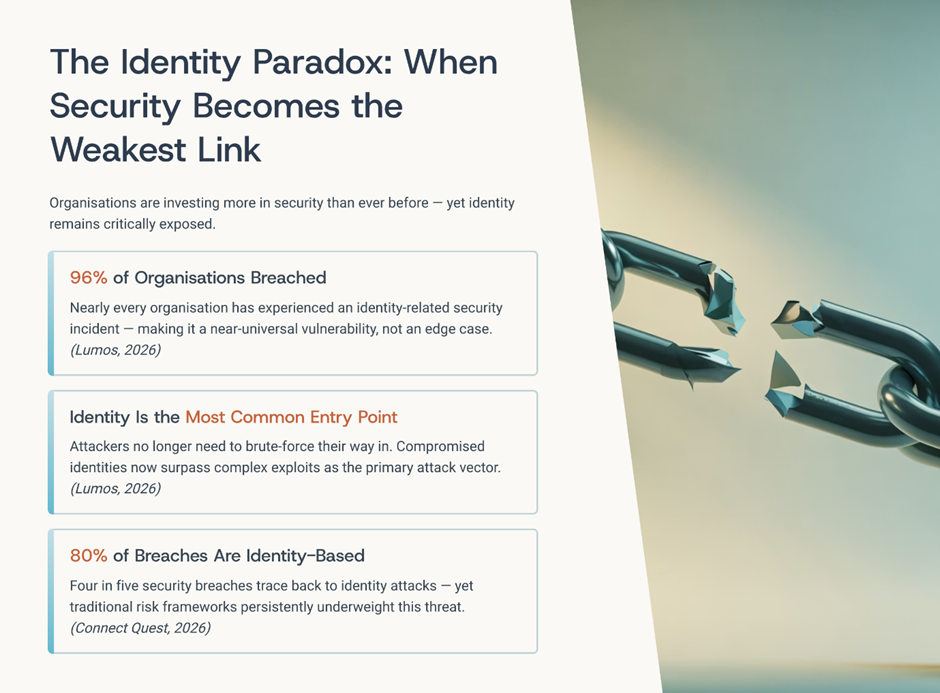
Across industries and geographies, a clear and consistent pattern is emerging; identity is no longer just a component of cybersecurity; it is at the centre of it.
- A large majority of breaches involve stolen or compromised credentials
Attackers increasingly rely on credential theft because it allows them to bypass traditional security layers. Instead of triggering alarms, they appear as legitimate users, making detection significantly harder. - Phishing and social engineering remain dominant entry points
Despite advancements in security technologies, human behaviour continues to be a critical vulnerability. Carefully crafted phishing campaigns and social engineering tactics are enabling attackers to harvest credentials at scale. - MFA fatigue attacks and identity misuse are rising
Attackers are now exploiting authentication mechanisms themselves. By overwhelming users with repeated authentication requests, they manipulate human response patterns to gain access. - Supply chain attacks increasingly exploit trusted access
Rather than targeting organisations directly, attackers compromise vendors or partners and leverage their trusted identities to infiltrate multiple systems simultaneously.
What This Means for Leadership
Attackers are no longer bypassing systems.
They are leveraging identities to operate within them.
Examples of Identity-Centric Risks
- Compromised employee credentials leading to ransomware deployment
- Third-party vendor access enabling lateral movement
- Service accounts and APIs are being exploited due to a lack of visibility
- Privileged accounts used without detection
V. Where Organisations Are Struggling
From a leadership standpoint, IAM challenges are not just technical; they are structural.
1. Lack of Visibility Across Identities
Most organisations cannot confidently answer:
- Who has access to what systems?
- Why do they have that access?
- Should they still have it?
2. Identity Sprawl
Modern enterprises deal with:
- Employees across multiple geographies
- Contractors and gig workers
- Third-party vendors
- Machine identities (APIs, bots, service accounts)
This creates thousands, sometimes millions, of identities.
3. Overprivileged Access
- Users accumulate access over time
- Role changes are not reflected in permissions
- Least privilege is rarely enforced consistently
Result:
A single compromised identity can have a disproportionate impact.
4. Fragmented Systems
IAM often operates across:
- Legacy systems
- Cloud platforms
- SaaS applications
Without integration, governance becomes inconsistent and reactive.
5. Third-Party Risk Blind Spots
- Vendors often have persistent access
- Limited monitoring of third-party activities
- Weak enforcement of identity controls outside the organisation
VI. Why IAM Is Becoming Central to Enterprise Risk Management
1. Identity Directly Impacts Business Risk
IAM is no longer an IT metric; it is a business risk indicator.
- Unauthorized access → Data breach
- Privilege misuse → Financial loss
- Identity compromise → Operational disruption
2. Regulatory Pressure Is Increasing
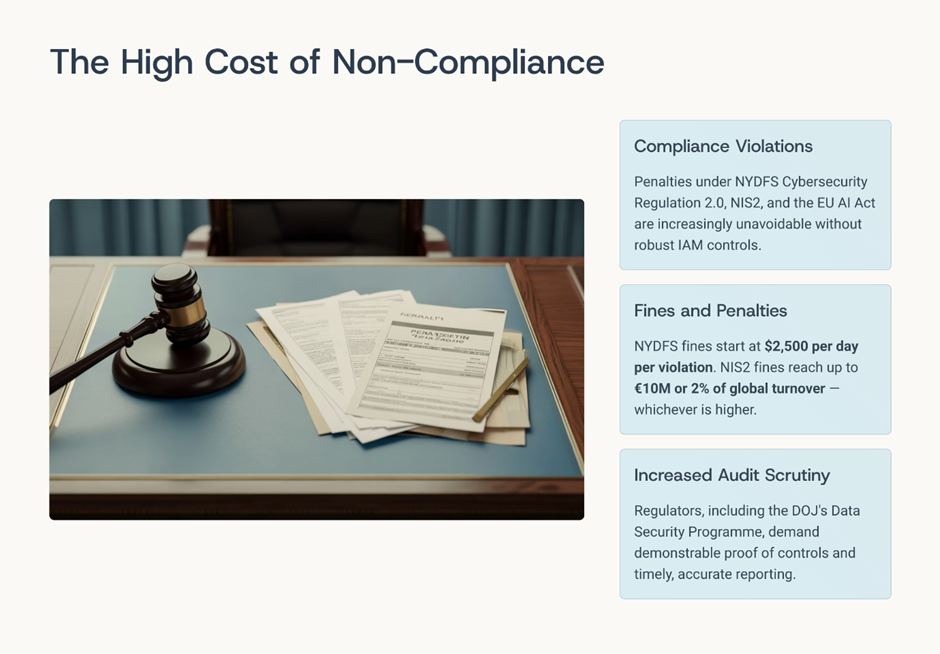
Global regulations now emphasise:
- Access governance
- Identity lifecycle management
- Auditability of access decisions
Organisations without strong IAM face:
- Compliance violations
- Fines and penalties
- Increased audit scrutiny
3. Cloud and Digital Transformation Depend on IAM

As enterprises move to the cloud:
- Traditional perimeter controls weaken
- Identity becomes the primary control layer
Without IAM maturity:
- Digital transformation introduces uncontrolled risk
4. Zero Trust Architecture Relies on IAM

Zero Trust is built on one principle:
Never trust. Always verify.
IAM enables:
- Continuous authentication
- Context-aware access
- Least privilege enforcement
5. Supply Chain Security Is Identity-Driven
Modern ecosystems include:
- Vendors
- Partners
- SaaS providers
IAM ensures:
- Controlled third-party access
- Monitoring of external identities
- Reduction of supply chain risk
VI. Leadership Approach: How CXOs Must Respond
IAM must move from operational function to strategic priority.
1. Treat IAM as a Business Control
- Align IAM with enterprise risk frameworks
- Integrate IAM into board-level discussions
- Establish clear ownership and accountability
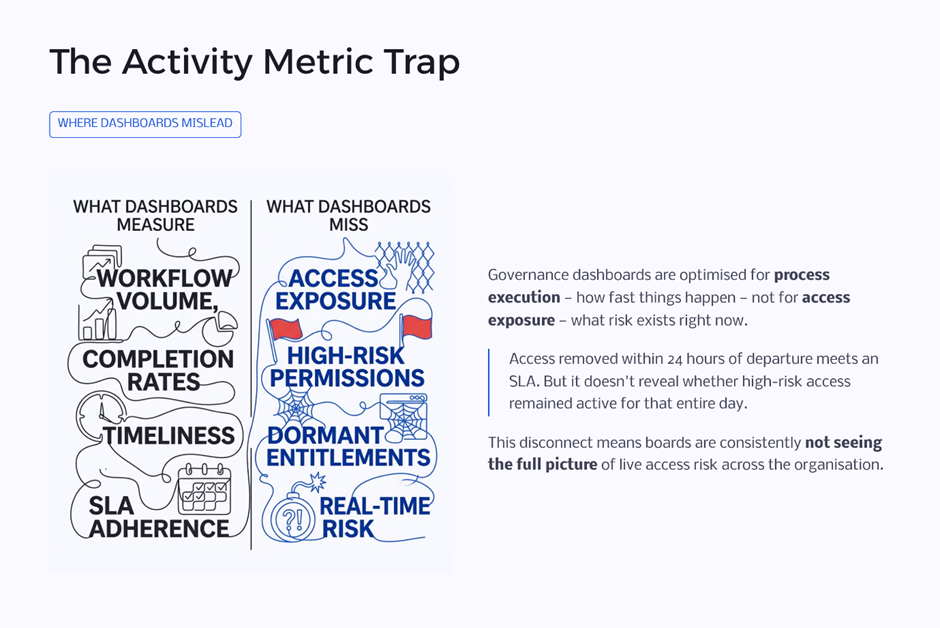
2. Shift from Periodic to Continuous Governance
- Replace annual access reviews with continuous monitoring
- Use automation for real-time access decisions
3. Enforce Least Privilege at Scale
- Implement role-based and attribute-based access models
- Regularly review and adjust access rights
4. Extend IAM to Third-Party and Machine Identities
- Apply the same governance standards to:
- Vendors
- APIs
- Bots
- Monitor all non-human identities
5. Invest in Intelligence-Driven IAM
- Use AI for anomaly detection
- Identify unusual access patterns
- Detect insider threats early
VIII. Future Risk Landscape: What Lies Ahead
IAM will play an even greater role in managing emerging risks.
1. AI-Driven Identity Attacks
- Automated phishing campaigns
- Deepfake impersonation
- Credential harvesting at scale
2. Explosion of Machine Identities
- APIs and bots outnumber human users
- Many remain unmanaged and unmonitored
3. Decentralised Work Environments
- Remote work expands access points
- Increased reliance on identity-based controls
4. Increasing Regulatory Expectations
- Governments demanding identity transparency
- Stronger compliance requirements around access
Key Metrics Every CXO Should Track
To elevate IAM into ERM, leadership must focus on measurable indicators:
- Percentage of overprivileged users
- Number of inactive or orphaned accounts
- Time to revoke access after role change
- Coverage of access certifications
- Third-party access exposure
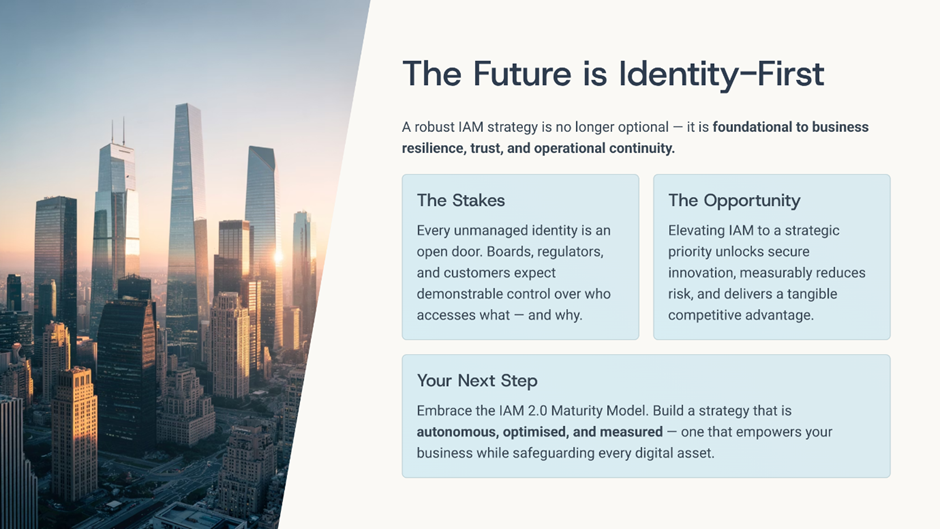
IX. The Strategic Opportunity: Beyond Risk Mitigation
IAM is not just about reducing risk; it enables growth.
Business Benefits of Strong IAM
- Faster onboarding and access provisioning
- Improved operational efficiency
- Stronger customer and partner trust
- Better compliance posture
Secure digital transformation
X. From Control Function to Strategic Enabler
From a CXO perspective, the message is clear:
IAM is no longer a backend system.
It is the central nervous system of enterprise risk management.
Organisations that fail to recognise this shift will continue to invest in security, while leaving their most critical vulnerability exposed.
Those that embrace IAM as a strategic control will:
- Strengthen resilience
- Enable innovation
- Build trust in an increasingly digital economy